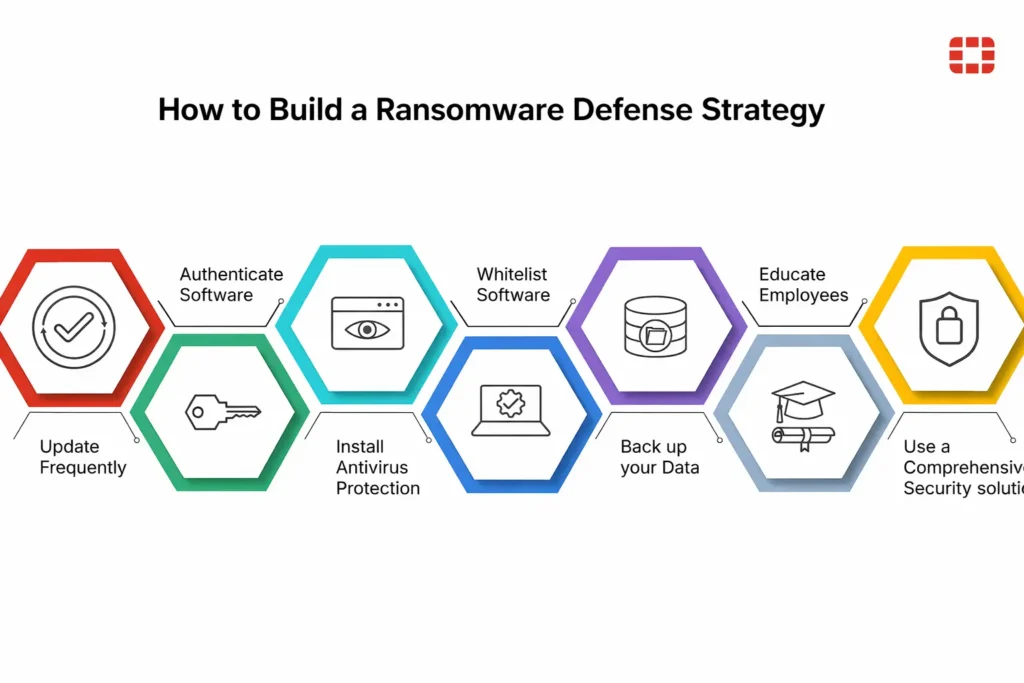
Ransomware attacks rarely happen by accident. In most cases, attackers exploit weak passwords, outdated software, or careless clicks. That’s why building a ransomware defense strategy requires more than just installing security tools. It means understanding risks, protecting critical systems, and preparing your team to respond quickly. When organizations combine strong technology, smart policies, and well-trained employees, they dramatically reduce the chances that ransomware will disrupt operations or lock them out of their own data.
Table of Contents
ToggleStart with a Comprehensive Risk Assessment
Before you build any ransomware defense strategy, you need to understand what you’re actually protecting. That means identifying critical systems, sensitive data, and tools your organization relies on every single day. Think about databases, customer records, financial systems, and internal platforms. Once you list these assets clearly, you can start focusing on protection where it actually matters.
A ransomware attack rarely begins with the systems you expect. Instead, attackers look for the easiest way inside. That’s why mapping possible entry points matters so much. Phishing emails, weak passwords, exposed remote desktop services, and outdated software often become the first entry points attackers try to exploit.
Many companies believe their defenses already cover everything, yet a closer look often tells a different story. Reviewing your current tools, policies, and procedures reveals where gaps exist. Sometimes, a managed security service provider can help analyze this setup objectively and identify weak spots that internal teams may overlook.
Once you understand your environment, you need to prioritize what deserves immediate protection. Not every system carries the same risk or business impact. If attackers encrypt your accounting platform, operations may slow down. If they encrypt your production database, the entire business may stop. Ranking assets by importance helps you allocate security resources much more effectively.
Strengthen Endpoint and Network Protection
Every device connected to your network can become a potential ransomware entry point. Laptops, desktops, and even servers represent targets if they lack proper monitoring. Modern endpoint detection and response tools track suspicious behavior and stop attacks early. They look beyond traditional antivirus signatures and identify unusual activity before real damage occurs.
Network segmentation plays a huge role in limiting how far attackers can travel once they gain access. Instead of allowing unrestricted communication between systems, you divide networks into smaller zones. That way, if ransomware hits one area, it cannot automatically spread to every other system connected to the environment.
Access control matters just as much as technical defenses. Many organizations accidentally give employees far more permissions than they actually need. By enforcing least-privilege access policies, you reduce the damage any compromised account can cause. Even if attackers steal credentials, limited permissions prevent them from taking full control.
Watching network traffic closely often reveals early warning signs. Unusual data transfers, unfamiliar connections, or strange login patterns may signal an ongoing attack attempt. When security teams monitor these patterns continuously, they can respond quickly and isolate suspicious activity before ransomware spreads across the infrastructure.
Establish Reliable Backup and Recovery Procedures
Backups represent the last line of defense when ransomware slips past preventive measures. However, simply having backups isn’t enough. Organizations must store copies of critical systems regularly and ensure those backups remain isolated from the main environment. If attackers can reach backup servers, they often encrypt those too.
Many companies assume backups will work perfectly during a crisis, yet they rarely test them. Recovery drills help verify that data actually restores correctly and that teams understand the process. Practicing restoration under realistic conditions reduces confusion when a real incident forces you to recover quickly.
Separating backup environments from production networks adds another layer of protection. Storing copies offline or using immutable storage prevents attackers from altering or deleting them. Even if ransomware compromises your primary systems, these protected backups remain untouched and ready to restore operations.
Clear recovery objectives also help organizations respond faster during an incident. Recovery time objectives define how quickly systems must return online, while recovery point objectives determine how much data loss remains acceptable. Establishing these expectations beforehand helps teams prioritize which systems to restore first.
Train Employees to Recognize and Prevent Threats
Technology alone cannot stop ransomware. Human behavior plays a huge role in whether an attack succeeds or fails. Employees interact with emails, files, and links all day long, which makes them the first line of defense. When they recognize suspicious messages early, they can stop an attack before it spreads.
Phishing emails remain one of the most common ransomware delivery methods. Attackers design messages that look legitimate and often create urgency to trick recipients into clicking links or downloading attachments. Training sessions that demonstrate real examples help employees recognize these tactics and avoid falling for them.
Organizations also benefit from creating clear reporting channels for suspicious activity. When employees know exactly where to send questionable emails or files, they report them faster. Quick reporting allows security teams to investigate immediately and warn the rest of the organization if a broader phishing campaign appears.
Simulation exercises strengthen awareness even further. By running controlled phishing tests or mock ransomware scenarios, organizations observe how employees react under pressure. These exercises reveal knowledge gaps while reinforcing good security habits, helping teams build stronger defensive instincts over time.
Create a Clear Incident Response Plan
No organization wants to deal with ransomware, yet preparation makes a huge difference when it happens. A well-structured incident response plan outlines exactly who takes action, what steps teams follow, and how decisions get made. Without that structure, panic and confusion often slow the response.
Clear roles and responsibilities help teams move quickly during an incident. Security specialists focus on containment and investigation, while leadership manages communication and operational decisions. When everyone understands their role beforehand, the response process runs far more smoothly under pressure.
Communication also becomes critical during ransomware events. Internal teams need regular updates, while external communication may involve customers, regulators, or partners. Establishing escalation paths ensures the right people receive information quickly and can coordinate responses across departments.
Containment and remediation procedures form the core of the response plan. Teams must isolate affected systems, investigate how attackers entered the network, and remove malicious access. Having predefined workflows helps security teams act decisively rather than improvise as the attack unfolds.
Wrap Up
A strong ransomware defense strategy doesn’t rely on a single tool or quick fix. Instead, it combines prevention, monitoring, backups, and employee awareness into one coordinated approach. Organizations that continuously evaluate risks, strengthen protections, and prepare for incidents stay far more resilient. While no system can eliminate risk entirely, consistent preparation makes it much harder for attackers to succeed and much easier for teams to recover quickly if an incident occurs.